2026-04-03 16:00:56
One of the pitfalls of modern engineering is that it’s entirely possible to end up in a situation where a product or solution has been designed by someone who has never left a desk. Which wouldn’t be a problem if things didn’t have a tendency to work differently in real life than they do in theory.
One of those things is automatic chicken coop doors, which have to operate reliably in not only a wide range of climates but with a number of possible physical limitations as well. [Vinnie] has taken on the challenge of building one which actually accomplishes all of these tasks, after realizing that the off-the-shelf solutions were victims of design over practicality.
 [Vinnie] designed this door to be operated by the one thing that’s always 100% reliable: gravity. A linear actuator lifts the door at the beginning of the day, and then at night it’s allowed to fall back down in its track. A latch secures it against smarter intruders like raccoons. [Vinnie] has found that this lifting mechanism holds up much better in mud, snow, ice, and other difficult conditions than any other method he’s tried so far.
[Vinnie] designed this door to be operated by the one thing that’s always 100% reliable: gravity. A linear actuator lifts the door at the beginning of the day, and then at night it’s allowed to fall back down in its track. A latch secures it against smarter intruders like raccoons. [Vinnie] has found that this lifting mechanism holds up much better in mud, snow, ice, and other difficult conditions than any other method he’s tried so far.
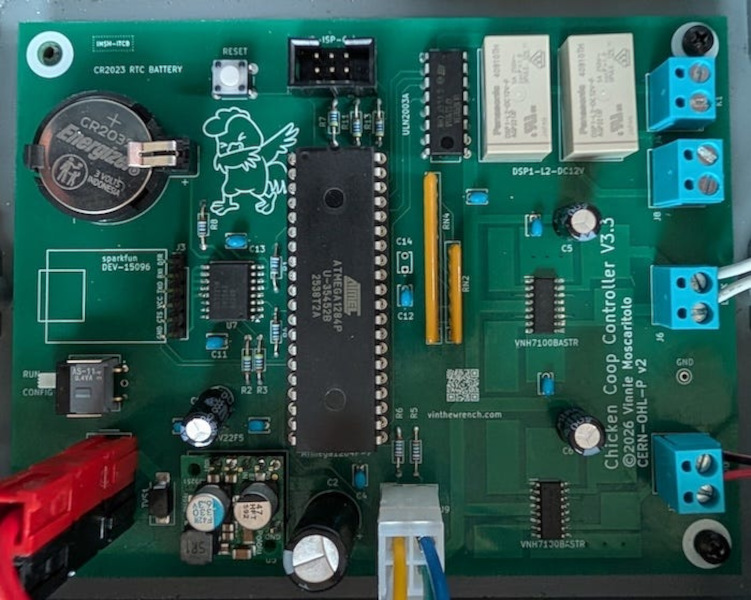
The system is built around a ATmega1284P, and calculates the sunrise and sunset times each day to know when to open or close the door. He’s built the system as a state machine which makes it more robust during power outages, which is a necessity since his chicken coop is mobile and is frequently out of range of WiFi and is battery powered.
The approach [Vinnie] takes to automation is something that has application outside of his own farmstead. Using state machines instead of schedules, ensuring the design is as simple as possible and works within its environment, and minimizing reliance on electric and data infrastructure can go a long way to solving problems that might not appear when designing something on paper.
He’s been automating many other things on his farm as well, and it’s worth checking it out if you haven’t seen it already.
2026-04-03 13:00:48
The topic of boiling water is apparently a rather divisive topic, with plenty of strong opinions to go around on what is safe and the most efficient way to go about it. Thus in a new video [Cahn] sought to address the many comments that came in after his previous testing of electric kettles on either 12 VDC or 240 VAC.
What’s interesting about this whole topic is that at its core the overall efficiency of boiling water is simply a matter of calculating the energy input minus energy losses, with the remaining energy going into the water.
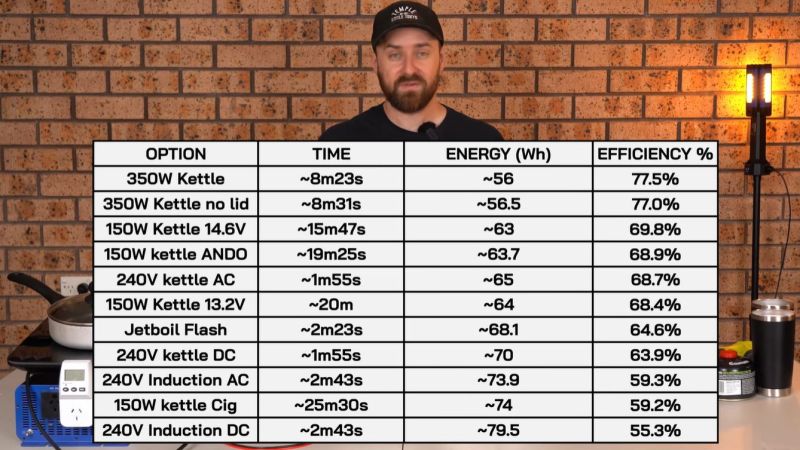
As we can see in the video, using a higher battery voltage doesn’t really change the efficiency of a 12 VDC kettle, but the higher current draw does manage to melt a fuse that can’t take the heat — requiring a 20 amp fuse instead of the 15 A one.
One change that does make a difference is how it’s connected. Replacing the thin gauge wiring and the attached cigarette lighter plug on the 12 VDC kettle with beefier cable and an Anderson plug made things run cooler, resulting in an efficiency bump of about 10%. This cut the time required to get the water boiling by around 6 minutes.
Added to this test were an induction hob and an iso-butane-powered Jetboil, both of which scored rather unimpressively. For the induction option it’s obvious that a lot of energy is wasted by having the pan radiate it away from the water, while burning iso-butane loses energy through the exhaust gases. Ultimately what you pick to boil water with should thus be mostly determined by convenience rather than sheer physics.
2026-04-03 10:00:23
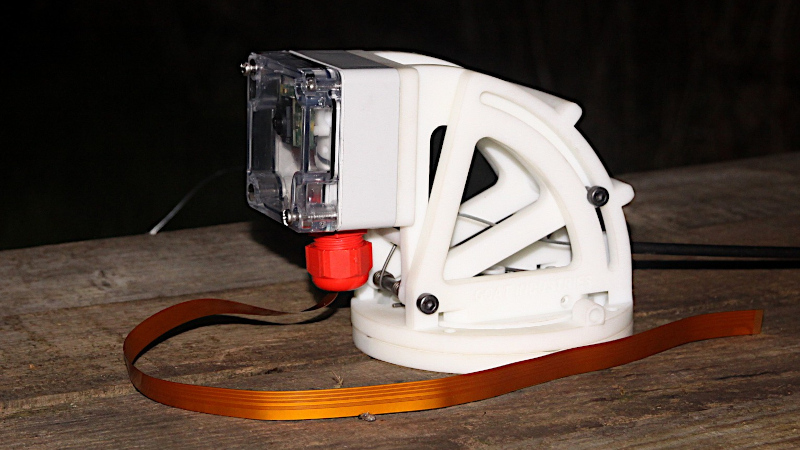
Over the years there have been many designs for pan-and-tilt camera mounts suitable for single board computer cameras. Often they mount small servos for the movement, but those in turn present problems when the device finds its way outdoors. [GOAT Industries] is here with a novel solution to this problem, instead of trying to cover up the servos on the mount itself, the whole thing is remotely controlled by linear actuators through Bowden cables.
Testing was performed using Mole-Grips instead of actuators, and revealed a few design quirks. There are hefty springs to provide tension, and since they work against 3D printed assemblies those in turn have to be reinforced. The layout of the Bowden cable run is also important, as it has a bearing on the amount of springinesss in the system. But it provides a versatile pan-and-tilt mount for a Pi camera mounted in an IP-rated box, which is the object of the exercise.
For anyone wishing to build one the files can be found in a GitHub repository, and there’s a video below showing the device in action. Meanwhile it’s by no means the first pan-and-tilt head we’ve seen here at Hackaday, however many others are by necessity much more substantial affairs.
2026-04-03 07:00:56
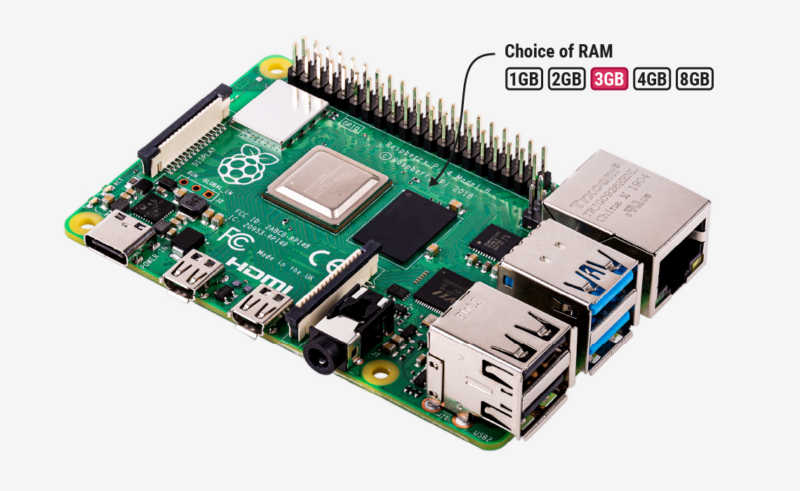
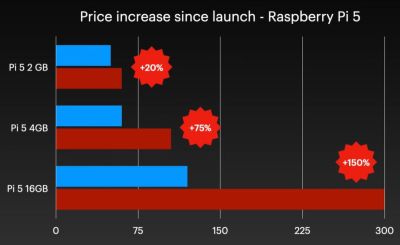
Although easily dismissed by some as another cruel April Fools joke, Raspberry Pi’s announcement of a new 3 GB model of the Raspberry Pi 4 along with (more) price increases for other models was no joke. Courtesy of the ongoing RAMpocalypse, supplies of LPDDR4 and LPDDR5 are massively affected, leading to this new RPi 4 model with two 1.5 GB LPDDR4 chips, as these are apparently cheaper to source.
Affected in this latest price increase across RP’s product range are RPi 4 and 5 models with 4 or more GB of RAM, with price bumps ranging from $25 on the low end to $150 for the Raspberry Pi 500+. If you wanted a Raspberry Pi 5 with 16 GB of RAM, you’re now paying $300 for the privilege.
Obviously, this news has got people like [Jeff Geerling] rather down in the dumps, essentially stating that using SBCs like the RPi is now beyond the means of many hobbyists. While you can still use SBCs that use e.g. LPDDR2 RAM, such as the older RPi Zero, 2 and 3 models, [Jeff] himself is now moving more towards wrangling with snakes on MCUs, as these boards are so far not significantly affected in terms of price.
With current projections in the RAM market being that this year will still see more price increases, it remains hard to tell exactly how ‘temporary’ this situation will be. That said, using readily available, powerful and cheap MCUs like the ESP32 variants for projects isn’t a bad idea if you really don’t need to be running more than perhaps FreeRTOS.
2026-04-03 04:00:11

If you’ve never heard of the threadless ball screw, which was invented over sixty years ago, [Angus] of Maker’s Muse has a video demonstrating the whole thing, covering its history and showcasing both its strengths and weaknesses. If you like seeing mechanical assemblies in action, give it a watch.
The device — consisting of little more than a smooth rod and three angled ball bearings — is a way to turn rotational motion into linear motion. Not a single belt, thread, or complex mechanical assembly in sight. While a simple nut on a threaded rod can turn rotation into linear motion, those come with their own issues. The threadless ball screw was one effort at finding a better way.
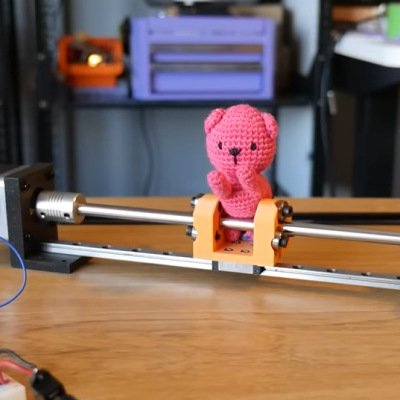
Threadless ball screws never really took off, although they were given some consideration for use in 3D printers back in the RepRap days. Today one can purchase quality CNC components without leaving one’s web browser, but back in the early 2000s things like lead screws and ball screws were rather more specialized, less accessible, and more expensive than they are today. RepRap folks had to make their own solutions. But while the threadless ball screw is a very DIY-friendly design, it was ultimately lacking in performance.
The main problem is they’re just not precise enough for anything like CNC work. [Angus] does some back-and-forth tests with a 3D printed unit that shows serious drift after only a few minutes. Now, he knows perfectly well that his 3D-printed test unit is far from ideal, but the rapidity at which it drifted was still a surprise. Making a carriage with two threadless ball screws — one at each end — performed a lot better, but was ultimately still flawed.
It’s not all bad. There’s zero backlash. They are mechanically simple, remarkably smooth, and utterly quiet. Also, [Angus] discovered that the maximum force this setup can be made to apply is surprisingly significant, and is directly related to the tension on the bearings. That means one can trivially adjust how easily the carriage slips (or doesn’t) just by tightening or loosening the screw holding each bearing.
Sure, they’re not precise. But maybe you don’t need precision. Maybe you just need to move something back and forth in a strong & silent sort of way that can still slip gracefully (and quietly) if something goes awry, like bottoming out an axis. 3D printing makes it pretty easy to whip one up, so maybe there’s still a place for the threadless ball screw.
2026-04-03 02:30:58

Although Windows 95 stole the show, Windows 3.0 was arguably the first version of Windows that more or less nailed the basic Windows UI concept, with the major 3.1 update being quite recognizable to a modern-day audience. Even better is that you can still install Win3.1 on a modern x86-compatible PC and get some massive improvements along the way, as [Omores] demonstrates in a recent video.
The only real gotcha here is that the AMD AM5 system with Asus Prime X670-P mainboard is one of those boards whose UEFI BIOS still has the ‘classic BIOS’ Compatibility Support Module (CSM) option. With that enabled, Win 3.1 installs without further fuss via a USB floppy drive from a stack of ‘backup’ floppies that someone made in the early 90s. [Omores] also tried it with CSMWrap, but with this USB to PS/2 emulation didn’t work.
Windows 3.1 supports ‘enhanced mode’ by default, which adds virtual memory and multi-tasking if you have an 80386 CPU or better. To fix crashing on boot and having to use ‘standard mode’ instead, the ahcifix.386 fix for the responsible SATA issue by [PluMGMK] should help, or a separate SATA expansion card.
For the video driver the vbesvga.drv by [PluMGMK] was used, to support all VESA BIOS Extensions modes. This driver has improved massively since we last covered it and works great with an RTX 5060 Ti GPU. There’s now even DCI support to enable direct GPU VRAM access for e.g. video playback, with audio also working great with only a few driver-related gotchas.