2026-05-13 22:47:17
Three years ago, startup founders loved showing off their AI stack like it was a trophy shelf. A writing tool here, a chatbot there. Maybe an automation layer stitched together with good intentions and a prayer. It looked impressive in investor decks and sounded even better on podcasts. Then reality caught up.
Teams learned the hard way that collecting AI tools doesn’t magically create leverage. It often creates noise, overlap, extra cost, and one more thing nobody really owns. In 2026, the startups pulling ahead aren’t the ones with the longest tool list. They’re the ones that figured out what AI is actually supposed to do inside a business, and built around that with ruthless clarity.
function getCountryUnicodeFlag(countryCode) { return countryCode.toUpperCase().replace(/./g, (char) => String.fromCodePoint(char.charCodeAt(0) + 127397)) };
// HTML sanitization function to prevent XSS function sanitizeHtml(str) { if (typeof str !== 'string') return ''; return str .replace(/&/g, '&') .replace(/, '<') .replace(/>/g, '>') .replace(/"/g, '"') .replace(/'/g, ''') .replace(/\//g, '/'); }
// URL sanitization function to prevent javascript: and data: URLs function sanitizeUrl(url) { if (typeof url !== 'string') return ''; const trimmedUrl = url.trim().toLowerCase(); if (trimmedUrl.startsWith('javascript:') || trimmedUrl.startsWith('data:') || trimmedUrl.startsWith('vbscript:')) { return '#'; } return url; }
const getBrowserLanguage = () => { if (!window?.navigator?.language?.split('-')[1]) { return window?.navigator?.language?.toUpperCase(); } return window?.navigator?.language?.split('-')[1]; };
function getDefaultCountryProgram(defaultCountryCode, smsProgramData) { if (!smsProgramData || smsProgramData.length === 0) { return null; }
const browserLanguage = getBrowserLanguage();
if (browserLanguage) { const foundProgram = smsProgramData.find( (program) => program?.countryCode === browserLanguage, ); if (foundProgram) { return foundProgram; } }
if (defaultCountryCode) { const foundProgram = smsProgramData.find( (program) => program?.countryCode === defaultCountryCode, ); if (foundProgram) { return foundProgram; } }
return smsProgramData[0]; }
function updateSmsLegalText(countryCode, fieldName) { if (!countryCode || !fieldName) { return; }
const programs = window?.MC?.smsPhoneData?.programs; if (!programs || !Array.isArray(programs)) { return; }
const program = programs.find(program => program?.countryCode === countryCode); if (!program || !program.requiredTemplate) { return; }
var smsConsentHtmlRenderingFixEnabled = true;
const legalTextElement = document.querySelector('#legal-text-' + fieldName); if (!legalTextElement) { return; }
const divRegex = new RegExp('?[div][^>]*>', 'gi');
const blockWrapperRegex = new RegExp('?(?:div|p)[^>]*>', 'gi');
const fullAnchorRegex = new RegExp('
const template = smsConsentHtmlRenderingFixEnabled ? program.requiredTemplate .replace(/\s*
]*>/gi, ' ') .replace(blockWrapperRegex, '') : program.requiredTemplate.replace(divRegex, '');
legalTextElement.textContent = ''; const parts = template.split(/(.*?)/g); parts.forEach(function(part) { if (!part) { return; } const anchorMatch = part.match(/(.*?)/); if (anchorMatch) { const linkElement = document.createElement('a'); linkElement.href = sanitizeUrl(anchorMatch[1]); linkElement.target = sanitizeHtml(anchorMatch[2]); linkElement.textContent = sanitizeHtml(anchorMatch[3]); legalTextElement.appendChild(linkElement); } else { legalTextElement.appendChild(document.createTextNode(part)); } });
}
function generateDropdownOptions(smsProgramData) { if (!smsProgramData || smsProgramData.length === 0) { return ''; }
var programs = false ? smsProgramData.filter(function(p, i, arr) { return arr.findIndex(function(q) { return q.countryCode === p.countryCode; }) === i; }) : smsProgramData;
return programs.map(program => { const flag = getCountryUnicodeFlag(program.countryCode); const countryName = getCountryName(program.countryCode); const callingCode = program.countryCallingCode || ''; // Sanitize all values to prevent XSS const sanitizedCountryCode = sanitizeHtml(program.countryCode || ''); const sanitizedCountryName = sanitizeHtml(countryName || ''); const sanitizedCallingCode = sanitizeHtml(callingCode || ''); return ''; }).join(''); }
function getCountryName(countryCode) { if (window.MC?.smsPhoneData?.smsProgramDataCountryNames && Array.isArray(window.MC.smsPhoneData.smsProgramDataCountryNames)) { for (let i = 0; i
A lot of startups treated (and still do) AI adoption like a shopping spree. Someone added a meeting summarizer. The very next day, marketing picked a content generator, while ops added an automation platform.
Product started testing copilots that annotate data without human input. Before long, every team had its own favorite tool, its own workflow, and its own subscription line item quietly expanding in the background.
The result looked modern from the outside, but inside, it was messy. Founders were paying for five tools that solved variations of the same problem. Employees were copying work from one system into another because the integrations were shallow. Nobody had a clear view of what was saving funds, what was creating risk, and what was just making people feel productive.
That’s the first big shift in 2026. Startups have stopped mistaking tool adoption for operational maturity. The conversation has moved away from what AI apps a team uses and toward what parts of the company can reliably run faster, cheaper, and better because agents are embedded in the workflow itself.
There’s been a quiet rebellion against dashboard fatigue. Teams got tired of bouncing between tools, checking different reports, and trying to piece together what was actually happening in the business. AI didn’t solve that problem when it arrived as one more tab.
What’s working now is a move toward owned systems. Startups are choosing platforms and workflows they can shape around their actual brand. They want fewer black boxes and fewer brittle chains of integrations that fall apart the second one vendor changes a feature.
That doesn’t always mean building everything from scratch. Most early-stage companies still rely on third-party tools, and that’s fine. What changed is the mindset. There’s more skepticism around renting critical thinking from a SaaS vendor whose roadmap may have nothing to do with your company’s needs.
In practical terms, that means startups are prioritizing infrastructure they can understand, adapt, and govern. The old stack mentality encouraged accumulation. The 2026 mindset rewards control.
One of the clearest signs of maturity is that the best AI systems barely announce themselves. Nobody in a healthy startup wants to stop mid-workflow and admire the machinery. They want things to work.
When AI is doing its job well, all the skills gaps get patched subtly, but effectively. Founders get sharper weekly summaries without asking for them. Sales reps enter fewer manual updates because of automated fintech tools humming in the background. Marketers move from brief to draft faster because the system already knows the brand voice, target segment, and campaign context. It feels less like using AI and more like the company itself got quicker.
That invisibility matters. Employees are exhausted by software that demands attention instead of reducing friction. Founders are learning that adoption goes up when AI feels like part of the operating environment, not a special event.
That’s one reason the loudest AI products often end up less valuable than expected. They ask users to adapt too much. The startups winning in 2026 are adapting the system to the team.
Take free expert-led courses and unlock access to tools, mentorship, networking, and Verizon grant opportunities for small businesses.
Trust has become one of the most practical business filters in the AI era. Startups now care a lot more about where outputs come from, who can verify them, what data is being touched, and what happens when the model gets something wrong.
A year or two ago, plenty of teams were willing to overlook those questions because speed felt more urgent. Now the cost of bad outputs is clearer. A hallucinated insight in finance, a sloppy answer in customer support, or a rogue automation in operations can create a data mess faster than any founder wants to clean up.
That’s why trust is shaping the modern stack more than novelty. Teams want auditability. They want permissions. They want systems that can show their work, stay inside the right guardrails, and fail in ways humans can catch. Reliability has become part of the product requirement, not a nice bonus.
The funny part is that this makes AI feel less magical and more useful, which is exactly the point.
It’s not a giant tower of AI subscriptions. It’s not a founder bragging about replacing half the company with agents. It’s not a trendy workflow copied from social media by someone who hasn’t looked closely enough at their own business.
What actually runs startups in 2026 is a tighter operating system that uses AI to win over new clients and instill trust. This means using automation only where repetition exists. Human judgment where nuance matters. But that doesn’t mean it should be taken for granted.
A future-proof startup in 2026 uses AI consciously and ethically. That’s what I call a model approach — AI embedded in the places where speed compounds and errors can be managed, not sprinkled everywhere for optics.
The strongest founders have become editors of complexity. They cut what doesn’t earn its place. They build systems that help people make better decisions without adding ceremony. They know the goal was never to become an AI startup in the aesthetic sense. The goal was to build a company that runs better.
That shift feels less glamorous than the old AI hype cycle, but it’s far more powerful. And it’s probably the first honest sign that the market is growing up.
Image by DC Studio on Magnific
The post Your AI Stack Is Already Obsolete. Here’s What Actually Runs Startups in 2026 appeared first on StartupNation.
2026-05-13 02:05:42
There’s a specific, quiet kind of panic that sets in for a founder when the early adopter surge begins to plateau. You’ve hit your first revenue milestones, the product is stable, and your initial customers are happy. Suddenly, the growth engine starts to sputter. Leads are harder to come by, and the sales cycle is stretching.
Many founders respond by increasing their ad spend or hiring more sales reps. However, the problem is rarely more marketing; it’s almost always related to positioning. As startups move from early-stage to early-growth, the messaging that won over your first 100 customers is rarely the same messaging that will win over the next 1,000. This is the Positioning Trap.
function getCountryUnicodeFlag(countryCode) { return countryCode.toUpperCase().replace(/./g, (char) => String.fromCodePoint(char.charCodeAt(0) + 127397)) };
// HTML sanitization function to prevent XSS function sanitizeHtml(str) { if (typeof str !== 'string') return ''; return str .replace(/&/g, '&') .replace(/, '<') .replace(/>/g, '>') .replace(/"/g, '"') .replace(/'/g, ''') .replace(/\//g, '/'); }
// URL sanitization function to prevent javascript: and data: URLs function sanitizeUrl(url) { if (typeof url !== 'string') return ''; const trimmedUrl = url.trim().toLowerCase(); if (trimmedUrl.startsWith('javascript:') || trimmedUrl.startsWith('data:') || trimmedUrl.startsWith('vbscript:')) { return '#'; } return url; }
const getBrowserLanguage = () => { if (!window?.navigator?.language?.split('-')[1]) { return window?.navigator?.language?.toUpperCase(); } return window?.navigator?.language?.split('-')[1]; };
function getDefaultCountryProgram(defaultCountryCode, smsProgramData) { if (!smsProgramData || smsProgramData.length === 0) { return null; }
const browserLanguage = getBrowserLanguage();
if (browserLanguage) { const foundProgram = smsProgramData.find( (program) => program?.countryCode === browserLanguage, ); if (foundProgram) { return foundProgram; } }
if (defaultCountryCode) { const foundProgram = smsProgramData.find( (program) => program?.countryCode === defaultCountryCode, ); if (foundProgram) { return foundProgram; } }
return smsProgramData[0]; }
function updateSmsLegalText(countryCode, fieldName) { if (!countryCode || !fieldName) { return; }
const programs = window?.MC?.smsPhoneData?.programs; if (!programs || !Array.isArray(programs)) { return; }
const program = programs.find(program => program?.countryCode === countryCode); if (!program || !program.requiredTemplate) { return; }
var smsConsentHtmlRenderingFixEnabled = true;
const legalTextElement = document.querySelector('#legal-text-' + fieldName); if (!legalTextElement) { return; }
const divRegex = new RegExp('?[div][^>]*>', 'gi');
const blockWrapperRegex = new RegExp('?(?:div|p)[^>]*>', 'gi');
const fullAnchorRegex = new RegExp('
const template = smsConsentHtmlRenderingFixEnabled ? program.requiredTemplate .replace(/\s*
]*>/gi, ' ') .replace(blockWrapperRegex, '') : program.requiredTemplate.replace(divRegex, '');
legalTextElement.textContent = ''; const parts = template.split(/(.*?)/g); parts.forEach(function(part) { if (!part) { return; } const anchorMatch = part.match(/(.*?)/); if (anchorMatch) { const linkElement = document.createElement('a'); linkElement.href = sanitizeUrl(anchorMatch[1]); linkElement.target = sanitizeHtml(anchorMatch[2]); linkElement.textContent = sanitizeHtml(anchorMatch[3]); legalTextElement.appendChild(linkElement); } else { legalTextElement.appendChild(document.createTextNode(part)); } });
}
function generateDropdownOptions(smsProgramData) { if (!smsProgramData || smsProgramData.length === 0) { return ''; }
var programs = false ? smsProgramData.filter(function(p, i, arr) { return arr.findIndex(function(q) { return q.countryCode === p.countryCode; }) === i; }) : smsProgramData;
return programs.map(program => { const flag = getCountryUnicodeFlag(program.countryCode); const countryName = getCountryName(program.countryCode); const callingCode = program.countryCallingCode || ''; // Sanitize all values to prevent XSS const sanitizedCountryCode = sanitizeHtml(program.countryCode || ''); const sanitizedCountryName = sanitizeHtml(countryName || ''); const sanitizedCallingCode = sanitizeHtml(callingCode || ''); return ''; }).join(''); }
function getCountryName(countryCode) { if (window.MC?.smsPhoneData?.smsProgramDataCountryNames && Array.isArray(window.MC.smsPhoneData.smsProgramDataCountryNames)) { for (let i = 0; i
The Symptom: The One-Size-Fits-All Message
Early on, startups tend to cast a wide net. You want anyone and everyone to use the product. As you scale, a broad message becomes scattered. If you’re trying to be the best solution for everyone, you end up being the specific solution for no one.
Data indicates that a significant portion of startup stagnation is due to a lack of communicating specific value to a specific segment. According to research from CB Insights, 43% of startups collapse because there’s poor product-market fit. Often, that misfit is actually a failure of the market to understand why they need you specifically.
The Diagnostic: The Resonance Gap
To identify if you’re stuck in the positioning trap, look for these three symptoms:
The Hidden Anchor: Solving for Positioning Debt
In the software world, technical debt refers to the implied cost of additional rework caused by choosing an easy, quick solution now instead of a better approach that would take longer. Startups face an identical challenge called Positioning Debt.
When you launched, you may have chosen a quick position to gain immediate traction. You were the Uber for X or the Cheapest Y. That debt served its purpose, and it got you through the door. As you scale into the early-growth phase, that old narrative begins to pull against your progress.
According to the Startup Genome Report, which analyzed over 3,200 startups, premature scaling is the top cause of failure, accounting for 74% of high-growth startup departures. Often, premature scaling is simply a startup trying to provide marketing gasoline for a brand narrative that hasn’t been upgraded to support a larger market.
The Founder’s Paradox: Why Great Products Have Bad Messaging
Founders are often too close to the solution to see the problem clearly. You spent years building the engine, so you want to talk about the horsepower and the pistons; however, your growth-stage customers only care about the destination. This cognitive bias creates messaging that’s inside-out: explaining what the company does rather than what the customer achieves.
Scaling requires a shift in perspective by moving from being the hero of the story to being the navigator. If your website is full of sentences starting with “We” or “Our,” you’re likely trapped in this paradox. Strategic positioning flips the script by making the customer the hero and your product the essential tool for their victory.
The Three Phases of the Positioning Pivot
Positioning is not a one-time event; it’s a lifecycle. Successful startups usually navigate three distinct pivots:
Understanding where you sit in this lifecycle prevents you from using early-stage language for a growth-stage challenge.
Take free expert-led courses and unlock access to tools, mentorship, networking, and Verizon grant opportunities for small businesses.
The High Cost of Positioning Inaction
Ignoring a positioning stall is an expensive mistake. When your messaging is scattered, your Customer Acquisition Costs (CAC) skyrocket. You’re essentially paying a “confusion tax” on every ad click and sales call. Your team spends more time explaining what the product is rather than closing deals.
Moreover, poor positioning attracts the wrong type of customers. These users often have higher churn rates and demand more from your support team because the product was never actually intended for their specific use case. Paying down your positioning debt now prevents a total collapse of your margins later.
A 5-Minute Positioning Audit for Founders
If you suspect your growth has stalled due to positioning, perform this quick audit of your primary landing page:
Actionable Steps to Re-Position for Growth
To bridge the gap from scattered to scaled, founders must evolve their brand umbrella: • Audit Your Customer Success Stories: Look at your top 10% of customers. What is the one specific problem you solved for them that no one else could? This is your White Space.
Key Takeaway
Stalling after early traction isn’t a sign of failure but rather a sign of evolution. Your original positioning was a ladder that got you to the first floor. To reach the roof, you need a different structure. By auditing your positioning, addressing your positioning debt, and tightening your focus, you can turn a plateau into a launchpad for the next phase of growth.
Image by garetsvisual on Magnific
The post Why Startups Stall After Early Traction: The Positioning Trap appeared first on StartupNation.
2026-05-07 01:00:27
Keeping a startup team motivated through turbulent times requires more than generic pep talks. This article presents 17 actionable strategies to sustain morale when resources are tight and uncertainty runs high, drawing on insights from experienced founders and leadership experts. These methods focus on transparency, recognition, and practical steps that acknowledge reality while building resilience.
function getCountryUnicodeFlag(countryCode) { return countryCode.toUpperCase().replace(/./g, (char) => String.fromCodePoint(char.charCodeAt(0) + 127397)) };
// HTML sanitization function to prevent XSS function sanitizeHtml(str) { if (typeof str !== 'string') return ''; return str .replace(/&/g, '&') .replace(/, '<') .replace(/>/g, '>') .replace(/"/g, '"') .replace(/'/g, ''') .replace(/\//g, '/'); }
// URL sanitization function to prevent javascript: and data: URLs function sanitizeUrl(url) { if (typeof url !== 'string') return ''; const trimmedUrl = url.trim().toLowerCase(); if (trimmedUrl.startsWith('javascript:') || trimmedUrl.startsWith('data:') || trimmedUrl.startsWith('vbscript:')) { return '#'; } return url; }
const getBrowserLanguage = () => { if (!window?.navigator?.language?.split('-')[1]) { return window?.navigator?.language?.toUpperCase(); } return window?.navigator?.language?.split('-')[1]; };
function getDefaultCountryProgram(defaultCountryCode, smsProgramData) { if (!smsProgramData || smsProgramData.length === 0) { return null; }
const browserLanguage = getBrowserLanguage();
if (browserLanguage) { const foundProgram = smsProgramData.find( (program) => program?.countryCode === browserLanguage, ); if (foundProgram) { return foundProgram; } }
if (defaultCountryCode) { const foundProgram = smsProgramData.find( (program) => program?.countryCode === defaultCountryCode, ); if (foundProgram) { return foundProgram; } }
return smsProgramData[0]; }
function updateSmsLegalText(countryCode, fieldName) { if (!countryCode || !fieldName) { return; }
const programs = window?.MC?.smsPhoneData?.programs; if (!programs || !Array.isArray(programs)) { return; }
const program = programs.find(program => program?.countryCode === countryCode); if (!program || !program.requiredTemplate) { return; }
var smsConsentHtmlRenderingFixEnabled = true;
const legalTextElement = document.querySelector('#legal-text-' + fieldName); if (!legalTextElement) { return; }
const divRegex = new RegExp('?[div][^>]*>', 'gi');
const blockWrapperRegex = new RegExp('?(?:div|p)[^>]*>', 'gi');
const fullAnchorRegex = new RegExp('
const template = smsConsentHtmlRenderingFixEnabled ? program.requiredTemplate .replace(/\s*
]*>/gi, ' ') .replace(blockWrapperRegex, '') : program.requiredTemplate.replace(divRegex, '');
legalTextElement.textContent = ''; const parts = template.split(/(.*?)/g); parts.forEach(function(part) { if (!part) { return; } const anchorMatch = part.match(/(.*?)/); if (anchorMatch) { const linkElement = document.createElement('a'); linkElement.href = sanitizeUrl(anchorMatch[1]); linkElement.target = sanitizeHtml(anchorMatch[2]); linkElement.textContent = sanitizeHtml(anchorMatch[3]); legalTextElement.appendChild(linkElement); } else { legalTextElement.appendChild(document.createTextNode(part)); } });
}
function generateDropdownOptions(smsProgramData) { if (!smsProgramData || smsProgramData.length === 0) { return ''; }
var programs = false ? smsProgramData.filter(function(p, i, arr) { return arr.findIndex(function(q) { return q.countryCode === p.countryCode; }) === i; }) : smsProgramData;
return programs.map(program => { const flag = getCountryUnicodeFlag(program.countryCode); const countryName = getCountryName(program.countryCode); const callingCode = program.countryCallingCode || ''; // Sanitize all values to prevent XSS const sanitizedCountryCode = sanitizeHtml(program.countryCode || ''); const sanitizedCountryName = sanitizeHtml(countryName || ''); const sanitizedCallingCode = sanitizeHtml(callingCode || ''); return ''; }).join(''); }
function getCountryName(countryCode) { if (window.MC?.smsPhoneData?.smsProgramDataCountryNames && Array.isArray(window.MC.smsPhoneData.smsProgramDataCountryNames)) { for (let i = 0; i
Deliver Hard News with Dignity
There is no harder moment in a startup than a layoff. Not just for the people losing their jobs, but for the ones who stay. Because once it happens, everyone left in the room is asking the same question, whether they say it out loud or not: am I next?
The answer has to be honest. Not optimistic. Not reassuring for the sake of keeping people calm. Honest. And it has to be backed by something real, because they are watching every word against every action that follows.
Years ago, I was consulting with a startup navigating a significant reduction in force. The decision was made to terminate everyone on a single group call. I counseled against it. What I watched was a room full of talented people absorbing one of the hardest moments of their professional lives with no space to fall apart, no privacy, no individual moment to simply be human. It was efficient. And it was one of the most dehumanizing things I have ever witnessed in a workplace.
When I later led my own reduction in force, I did it differently. Every conversation was one-on-one. Eye contact was available. People had space to fall apart, and so did the managers across from them. It was harder. It took more time. It was the only approach that allowed people to leave with their dignity intact.
The question I ask every leader I advise is simple: how would you want to receive this news? Give people a private moment. Tell them the truth about why. Hold space for them. This moment is not about the employer. It is entirely about the person sitting across from you.
Then comes the second obligation: the people who remain. They are not unaware. They are watching and calculating their own risk. Come back to them with the same honesty. If more change is possible, say it. If decisions are still being made, say that too. Tell them what you know, what you don’t, and when they will hear more. Then show up at that time with that information. Dragging people through repeated waves of uncertainty with no plan and no timeline is its own form of trauma.
The rule is the same for everyone: do what you say and say what you do. Morale does not recover because a leader is optimistic. It recovers because a leader is honest, consistent, and accountable, in that order.
Lena McDearmid, Founder, Wryver
Invite Ownership through Reality Sessions
The most difficult period for us came during our transition from a services model to building our fractional COO team. We had committed to scaling rapidly but were struggling to find the right operational leaders who could deliver our quality standards. For three months, I was working 80-hour weeks trying to cover gaps while maintaining client delivery.
Team morale was suffering because everyone felt the pressure. My existing team was picking up extra work, new hires were overwhelmed by unclear processes, and I was becoming the bottleneck for every decision. The breaking point came when two key team members approached me about burnout during the same week.
The approach that saved us was radical transparency combined with collaborative problem-solving. Instead of trying to shield my team from the challenges, I brought everyone together for what I called our “reality meeting.” I laid out exactly where we were, what wasn’t working, and admitted that I didn’t have all the answers.
But here’s what made the difference: instead of just dumping problems on them, I asked each person to identify one operational challenge they could help solve. Not additional work on top of their responsibilities, but problems they could tackle that would make their own jobs easier.
Our marketing coordinator streamlined our client onboarding process. Our project manager identified three recurring client questions that could be answered with better documentation. Our newest hire suggested a weekly team sync that would reduce constant Slack interruptions.
Within two weeks, we had implemented seven process improvements that came directly from the team. Morale shifted completely because instead of feeling like victims of a chaotic situation, everyone became part of the solution. People started looking forward to our weekly problem-solving sessions.
The measurable impact was immediate. Our client satisfaction scores actually improved during this difficult period because the team felt ownership over solutions rather than resentment about problems. Project delivery timelines stabilized because we were solving root causes instead of just working harder.
This experience shaped how I help founder clients navigate difficult periods. The instinct is to protect your team from challenges, but that actually disempowers them. When you involve people in solving problems, you tap into their creativity and transform a crisis into a team-building opportunity.
Derek Fredrickson, Founder & CEO, The COO Solution
Give Specific Genuine Recognition
The toughest stretch we went through taught me something I didn’t expect: people can handle bad news; what they can’t handle is being kept in the dark.
When things got hard, I stopped trying to package the situation nicely and just laid it out straight. What changed, what it meant for us, what was still in our hands, and where I needed the team’s help. That one shift changed the whole energy. People stopped waiting to be told what to do and started showing up with ideas and ownership.
But if I had to pick the single thing that worked best, it was specific, genuine recognition, especially in the worst weeks. Every Friday, I’d write short notes to people, calling out exactly what they did and why it mattered. Not “great job,” but “you caught that gap in the workflow, and it saved us three days.” Over time, people started doing it for each other, and that’s when I knew we’d be okay.
Alok Aggarwal, CEO & Chief Data Scientist, Scry AI
Talk about Failures Openly
In February 2025, our checkout platform for solo digital creators had just launched and new signups were coming in less than half the rate we projected we would. We had built the product for months, shipped it, but the numbers were flat for three straight weeks. Seeing those flat numbers day after day does something to a small team and I could feel the energy starting to drain out of everyone, including me.
So what I’ve done is conduct a 30-minute meeting each week with one agenda in mind: What went wrong this week and why. Not what went well. Not a progress update. Just failures which we talked about openly with all 5 of us on the call. The rule was simple: No blame and no fixing in the meeting. Just an honest accounting of what didn’t work. In the first three weeks, that meeting brought to the surface two messaging decisions that had been frustrating the team quietly for weeks, but nobody had brought up formally.
And that is why talking about failure out loud kept the morale higher than any win celebration ever did. Morale doesn’t shatter from bad results. It breaks from feeling like the people around you aren’t being straight about what’s actually happening, and that meeting removed that feeling completely.
Welly Mulia, Founder | Software & Creator Advocate, CartMango
Host an In-Person Reset
We invested in a short in-person get-together during one of our toughest periods. The budget wasn’t there, honestly — but we made it work because the team was burning out and Slack pep talks weren’t cutting it. We used the time to deliver the roadmap together, face to face. Not a party. A working session with real clarity on where we were headed. The shift was immediate. People left aligned, not just informed. What I learned is that during hard stretches, distributed teams need a physical reset — even a brief one. The cost felt painful at the time. Looking back, it was the cheapest retention move we made that year.
Maria Bakatsiuk, Founder & CMO, Maramio
Take free expert-led courses and unlock access to tools, mentorship, networking, and Verizon grant opportunities for small businesses.
Scale Down to Protect Capacity
My husband and I are the founders of our business. Running it from scratch means you feel every rough patch personally. It’s taken longer than I wish to say before I’ve learned to take better care of the team in those times.
What has helped us most is to scale down before it got too much. In rough patches, we temporarily stopped about 30% of non-critical projects, and spread work more equitably among the team. I stopped treating busyness as a badge of honor (honestly, that mindset was doing more damage than I realized), and that shift changed the whole tone.
Burnout is sneaky. People go slower and more silent and you notice it, too late. So I started catching it sooner and encouraged them to take their time off to actually rest.
That little tweak meant we retained all the techs for our busiest season. It’s cheaper to protect capacity than to replace it.
Emily Demirdonder, Director of Operations & Marketing, Proximity Plumbing
Display a Visible Progress Board
During our second year, we reached a stretch that put everything to the test. Our main distributor for cigars cut lead times without notice, delaying three confirmed launches of a product by six weeks. At the same time, our Meta ad account was flagged for tobacco-related content and our paid traffic became next to nothing overnight. Revenue for that month was 34% below our projected target. The team knew something was wrong and it was reflected in the energy in the room.
That is why I gave up trying to manage morale by talking to people and created something the team could see instead.
The problem with a difficult time is that people lose the sense that their day-to-day work is connected to anything going forward. They show up, do their tasks and go home with no idea if any of it mattered that day. We created a collective digital tracker for five daily metrics: new orders, new email subscribers, reviews received, social mentions and resolved customer issues. Every update on that board was proof that something moved because of what someone on the team did.
Two weeks of doing that, people started owning their portion of the board without being asked. A customer service rep would close down a complaint and make a log for it right away. Someone would take a new organic post and mark it. The team stopped feeling like they were waiting for the business to recover and started feeling like they were the ones recovering it, and that difference in mindset is what actually held the team together.
Brad Jackson, Director of Operations | eCommerce Founder, After Action Cigars
Create a Personal Shared Experience
During COVID, when our team was suddenly remote and morale was dipping from the isolation, I wanted to do something that felt personal rather than corporate. I sent everyone a curated bottle of wine and organized a virtual wine tasting together. It wasn’t about the wine itself — it was about creating a shared experience that reminded people we were still a team, even when we couldn’t be in the same room. That small gesture sparked real conversation, laughter, and connection. It taught me that during tough times, the most effective morale booster isn’t a grand strategy — it’s showing your team you’re thinking about them as people, not just employees. That one evening did more for our culture than any all-hands meeting could have.
Jeffrey Frese, Founder & CEO, Eat My face
Run Frank Weekly Check-Ins
During one of our toughest stretches, when deals were slowing and uncertainty was high, I realized quickly that silence from leadership creates more anxiety than the situation itself.
The single most effective approach I took was radical transparency paired with consistent communication.
I started hosting short weekly “state of the business” check-ins where I openly shared what we knew, what we didn’t, and what we were doing about it. No corporate spin. Just facts, direction, and reassurance. At the same time, I made sure to highlight small wins: new client conversations, team efforts, even incremental progress so people could see momentum wasn’t lost.
What made this work wasn’t just the information; it was trust. When your team understands the reality but also sees a clear path forward, they stay engaged instead of disengaged.
Morale didn’t improve overnight, but transparency turned uncertainty into alignment, and that’s what kept the team moving forward together.
Jim Griffith, CEO, Corporate Technologies LLC
Lead with Two-Way Honesty
I think the toughest stretch for my business was when we were in the middle of a big run of client growth, and our systems were not really built to handle the speed of that growth. Deadlines were piling up, stress levels were rising, and I was seeing the life drain out of the people I needed most. Rather than pushing harder or just masking the situation with more perks, I decided to be radically transparent.
I called the team together. I chose to be open about our situation and pressure points instead of giving a motivational speech. I asked the team, “What do you need from me right now?”
The single most impactful approach has been replacing assumptions with honest two-way dialogue. When people feel informed and heard instead of managed, they will invest in the solution rather than retreat from the problem. This approach also helped drive some tangible changes in terms of workload, based on actual capacity rather than assumption, and better communication checkpoints in the future.
To any founder facing a tough time, my advice would be: don’t lead with confidence at the expense of connection. Your team will go further with you if you lead from honesty than they will from bravado.
Cassandra May, Founder, Affordable Web Solutions
Expose Real Numbers for Clarity
The one thing that got my team through a difficult period was radical transparency. Not pep talks, not going out as a team. Just exposing people to the real numbers.
I used to try and protect my team from bad news. I thought shielding them from the hard parts of it was the right move as a founder. But what I realized was that I was making people more nervous by staying quiet rather than the actual situation ever did. When my team didn’t know what was going on, they filled in the gaps for themselves, and rarely in a good direction.
So on a slow growth period, I shared our real retention numbers, our pipeline and exactly what we needed to get through the quarter, without softening any of it.
My team didn’t panic. They got focused and started bringing solutions to the table because they finally understood what the actual problem was.
Transparency didn’t hurt morale. It replaced anxiety with direction.
Nikhil Pai, Founder, Chronicle Technologies
Publicly Celebrate Concrete Wins
I was transparent with my team about our situation to maintain morale. We lost three clients within six weeks and two of them left us in the same week. So, I got everyone on a call, shared our revenue number and told them straight what that number meant to us; no framing message and no “we’re going through a tough time.” Before that call, I could see people were slowing down their responses, sending shorter emails, people were not saying anything was wrong, but it was clear something wasn’t right. People tend to spiral into silence when they don’t know what’s going on, but once they had a clear understanding of what we were up against, they started working through the problem with me.
So, the approach that also worked really well was calling out wins publicly in our Slack channel. I posted every signed contract, great client review, every campaign that exceeded its goal, all posted publicly. It felt way too simple to work, but since I keep track of everything, I kept track of that too. In the first month, we averaged 4 shoutouts from the team, and in the second month we averaged 14. Both time to respond to issues and task completion increased by approximately 30% during the same two-month span. People needed to see evidence that the tide was changing and that’s what they got.
David Toby, Managing Director | Digital Marketing Specialist, Pathfinder Marketing
Hold a Candid Retrospective
During the slower period, we took a different approach to refresh and restart.
In our next all-hands meeting, we looked back at what we had gone through as a team. We revisited early product versions, the first users we acquired, and unsuccessful campaigns at first.
We also held an open AMA (ask me anything) session during the meeting to keep everything transparent. To encourage others to speak, I started by asking and answering a few tough questions myself. This encouraged others to share their concerns and ideas more openly.
All of this reminded everyone that progress had never been smooth and that we had confronted similar challenges together before.
Keeping this ritual helps us regain our energy and see our progress and the path forward clearly.
Musa Mustafa, CEO, VitaMail
Connect Work to Human Impact
We work in the food safety industry where the stakes are very real and very high, and what I’ve seen is that if there’s ever a drop in morale, it’s not for lack of care but because people lose sight of what they’re working towards.
Which is why right from the start, till today, our approach has always been focusing on what the actual impact of the work is. That’s more important for our morale than timelines, delays, or internal pressure. Because while that exists and is super important to ensure we do a great job, if that’s all you focus on, then it starts to feel like the whole job.
So to show our team how their work is helping lives and making food environments safer, we bring in real examples of where our detection kits are being used, what it was catching, and what contamination they actually prevented. It’s always very reaffirming to see your work helping the lives of others, which is why I feel safe to say, we’re very motivated and happy with what we do.
Mario Hupfeld, CTO and Co-Founder, NEMIS Technologies
Grant Micro-Budgets for Autonomy
Delegating the right to resolve problems, where they are defined, to junior members keeps the momentum going.
At the same time, spreading the control of the small operational budgets makes the individuals have some stake in the outcome. They have to be given actual financial power. Offering a more up-to-date worker a five hundred dollar checking fund keeps them fired up through slow quarters. Transferring the actual decision power down the organizational chain is an example of how executive leadership truly trusts the entire staff to see it through remarkably hard times.
Micro budgets do away with some of the daily friction of waiting to hear back on if the executive gets spending approved.
Small delays often ruin the drive of employees in an already stressful time. Giving a mid-range manager a specific three hundred dollar software allowance circumvents the usual red tape within the corporate procedures. They simply buy themselves the tools they need and get right back into work. In so many ways, taking yourselves out of small micro purchasing decisions frees up enormous sums of executive bandwidth. The staff has a sense of respect because no one questions the basic operational judgment of staff.
Autonomous spending limits are inherently educating junior staff to think with the cares of a business owner.
People treat company money differently when they get to filter the precise allocation. A five hundred dollar limit makes them be overly aggressive in negotiating with their vendors to stretch their funds. They naturally learn how to measure the return on investment on every single dollar of investment. As it turns out, providing people with strict boundaries creates extreme resourcefulness. The business gains the benefit of a staff with a financial understanding of operating their business and understanding profit margins almost intuitively.
Audit department spending and micro budgets for junior team members. Hand them the funds so they can repair immediate operational leakages themselves.
Travis Hoechlin, CEO, RizeUp Media
Invest in Regular Leadership Mentorship
During my startup journey, I experienced a lot of burnout, wearing every hat while self-funding my business when resources were limited. But knowing how important our energy is and realizing that the way I show up would set the tone for everyone around me, I knew I had to address how I was feeling. Committing to weekly coaching calls was the most effective approach; it kept me grounded, feeling supported, and able to think clearly even under pressure. I also incorporated wellness practices into my daily lifestyle, using breathwork and mini meditations to reset my energy so I could show up positive and consistent for my team.
Michi DeLucien, Founder, Certified Life & Energy Coach, Executive Operations Leader, Michi DeLucien Wellness, LLC
Prioritize Ruthlessly and Simplify
One thing that I really saw working for us during a tough situation was prioritizing what really needed our attention. We did this and cut out so much unnecessary noise and stress. Teams had clear targets, they knew what they were working towards even with all the chaos, and because of this, there was more stability, more focus, more motivation. So progress just became easier.
People tend to tackle challenges by going into this hyper communicative mode where they’re trying to communicate more, hold more meetings, send more emails. But actually, all this just creates more chaos and stress. You’re trying to solve everything at once and I’ve never seen that actually work.
So we keep it simple. We cut unnecessary communication and our updates are more structured so that people aren’t constantly hit with new information that they have to react to.
It’s easier to feel motivated when you feel like you’re moving forward, even if you’re only taking tiny steps and I feel like keeping things simple really helps keep this movement going.
Alex Sarellas, Managing Partner & CEO, PAJ GPS
Image by freepik
The post 17 Ways to Maintain Team Morale During Difficult Startup Periods appeared first on StartupNation.
2026-05-06 22:32:18
Remember 2021? VCs were throwing term sheets at anything with a pitch deck and a Notion board. Valuations were surreal, growth-at-all-costs was the only playbook in circulation, and bootstrapped founders were quietly dismissed as people who weren’t thinking big enough.
Then the correction hit. Founders who’d built lean, profitable businesses weren’t the underdogs anymore. They were the ones still standing. The bootstrapped hybrid model has been gaining serious ground ever since, and if you’re still using the same tools from three years ago, you might want to rethink your whole approach first.
function getCountryUnicodeFlag(countryCode) { return countryCode.toUpperCase().replace(/./g, (char) => String.fromCodePoint(char.charCodeAt(0) + 127397)) };
// HTML sanitization function to prevent XSS function sanitizeHtml(str) { if (typeof str !== 'string') return ''; return str .replace(/&/g, '&') .replace(/, '<') .replace(/>/g, '>') .replace(/"/g, '"') .replace(/'/g, ''') .replace(/\//g, '/'); }
// URL sanitization function to prevent javascript: and data: URLs function sanitizeUrl(url) { if (typeof url !== 'string') return ''; const trimmedUrl = url.trim().toLowerCase(); if (trimmedUrl.startsWith('javascript:') || trimmedUrl.startsWith('data:') || trimmedUrl.startsWith('vbscript:')) { return '#'; } return url; }
const getBrowserLanguage = () => { if (!window?.navigator?.language?.split('-')[1]) { return window?.navigator?.language?.toUpperCase(); } return window?.navigator?.language?.split('-')[1]; };
function getDefaultCountryProgram(defaultCountryCode, smsProgramData) { if (!smsProgramData || smsProgramData.length === 0) { return null; }
const browserLanguage = getBrowserLanguage();
if (browserLanguage) { const foundProgram = smsProgramData.find( (program) => program?.countryCode === browserLanguage, ); if (foundProgram) { return foundProgram; } }
if (defaultCountryCode) { const foundProgram = smsProgramData.find( (program) => program?.countryCode === defaultCountryCode, ); if (foundProgram) { return foundProgram; } }
return smsProgramData[0]; }
function updateSmsLegalText(countryCode, fieldName) { if (!countryCode || !fieldName) { return; }
const programs = window?.MC?.smsPhoneData?.programs; if (!programs || !Array.isArray(programs)) { return; }
const program = programs.find(program => program?.countryCode === countryCode); if (!program || !program.requiredTemplate) { return; }
var smsConsentHtmlRenderingFixEnabled = true;
const legalTextElement = document.querySelector('#legal-text-' + fieldName); if (!legalTextElement) { return; }
const divRegex = new RegExp('?[div][^>]*>', 'gi');
const blockWrapperRegex = new RegExp('?(?:div|p)[^>]*>', 'gi');
const fullAnchorRegex = new RegExp('
const template = smsConsentHtmlRenderingFixEnabled ? program.requiredTemplate .replace(/\s*
]*>/gi, ' ') .replace(blockWrapperRegex, '') : program.requiredTemplate.replace(divRegex, '');
legalTextElement.textContent = ''; const parts = template.split(/(.*?)/g); parts.forEach(function(part) { if (!part) { return; } const anchorMatch = part.match(/(.*?)/); if (anchorMatch) { const linkElement = document.createElement('a'); linkElement.href = sanitizeUrl(anchorMatch[1]); linkElement.target = sanitizeHtml(anchorMatch[2]); linkElement.textContent = sanitizeHtml(anchorMatch[3]); legalTextElement.appendChild(linkElement); } else { legalTextElement.appendChild(document.createTextNode(part)); } });
}
function generateDropdownOptions(smsProgramData) { if (!smsProgramData || smsProgramData.length === 0) { return ''; }
var programs = false ? smsProgramData.filter(function(p, i, arr) { return arr.findIndex(function(q) { return q.countryCode === p.countryCode; }) === i; }) : smsProgramData;
return programs.map(program => { const flag = getCountryUnicodeFlag(program.countryCode); const countryName = getCountryName(program.countryCode); const callingCode = program.countryCallingCode || ''; // Sanitize all values to prevent XSS const sanitizedCountryCode = sanitizeHtml(program.countryCode || ''); const sanitizedCountryName = sanitizeHtml(countryName || ''); const sanitizedCallingCode = sanitizeHtml(callingCode || ''); return ''; }).join(''); }
function getCountryName(countryCode) { if (window.MC?.smsPhoneData?.smsProgramDataCountryNames && Array.isArray(window.MC.smsPhoneData.smsProgramDataCountryNames)) { for (let i = 0; i
The post-2021 hangover wasn’t a temporary blip. Interest rates climbed, LPs got cautious, and VCs started asking uncomfortable questions about your financial strategy and analytics.
Founders who’d built their entire strategy around “raise, burn, raise again” found themselves stranded mid-flight, not knowing how to explain exactly how they intend to sell millions of monthly subscriptions of their AI tool. The runway wasn’t infinite, and suddenly, boards were asking why revenue wasn’t covering costs while the burn rate kept climbing every month.
What’s interesting is that the shift didn’t just scare founders away from traditional VC. It pushed a lot of them to rethink the whole model from scratch. Revenue-based financing, strategic angels, and hybrid approaches started getting serious attention. Founders were building differently because they had to, and a surprising number discovered they actually preferred it once they got there.
The data backs this up too. Profitable bootstrapped SaaS companies have been getting acquired at strong multiples, while VC-backed competitors at similar revenue levels have struggled to raise follow-on rounds. The narrative is shifting in real time, and the founders paying attention are adjusting accordingly.
The bootstrapped hybrid model has no official name or manifesto, but you know it’s different from bootstrapping when you see it. It’s more of a philosophy: grow on your own revenue as long as you realistically can, then bring in outside capital selectively and entirely on your terms. Basically, ou’re building something that can survive without one, and that changes how you approach every major decision.
In practice, it looks like a SaaS founder who bootstraps to $500k ARR before taking a small check from a strategic angel who opens doors rather than demands control. Africa’s current tech scene is the best example for this – despite $3 billion raised in 2026, the overall trend was towards stability and sustainability.
There’s a quiet confidence among bootstrapped and hybrid founders that’s hard to miss if you spend time in the right communities. They’re not anxious about the next raise. They’re not managing investor expectations every quarter or calibrating every product decision around metrics that look impressive in a board deck. They’re running businesses, and that distinction matters more than it sounds.
Profitability gives you leverage that VC-backed founders simply don’t have. You can say no to bad partnerships. You can take a slower, smarter path to hiring rather than stuffing headcount to signal momentum. You can go after markets that are genuinely interesting to you rather than markets that’ll look good in a Series A memo. That kind of optionality is worth more than most first-time founders realize.
It’s something you can only build when you’re not dependent on someone else’s capital to survive the next twelve months. More founders are figuring that out, and it shows in the type of companies getting built right now.
Take free expert-led courses and unlock access to tools, mentorship, networking, and Verizon grant opportunities for small businesses.
Let’s be straight about it: bootstrapping is slower. You can’t make aggressive bets on distribution when you’re funding growth from your own revenue. Competitors with VC backing can outspend you on marketing, talent, and product development in ways that are genuinely hard to counter in the short term. There’s no point pretending that part away.
But slower rarely means weaker. Slower usually means you’re building a customer base that actually sticks around, a product that earns its revenue month over month, and a team that learns to be efficient rather than just well-funded. When a VC-backed competitor burns through their Series B and hits layoffs, you’re not caught in the shockwave.
That kind of operational stability is a seriously underrated competitive advantage, especially in markets that are still finding their equilibrium. The companies still operating comfortably after the next correction will mostly be the ones that learned to grow without depending on the next check.
The honest answer is that it fits more businesses than most founders assume. If you’re building something with natural word-of-mouth, reasonable margins, and a product people actually need, there’s a real path to profitability without institutional capital from day one. The question worth sitting with is whether you need VC money to build the business, or just to grow faster than you otherwise would.
If it’s the latter, the hybrid approach deserves serious consideration. Take a strategic check when the timing and the terms make sense. Use revenue-based financing for capital-intensive moments like a product launch or a major hiring push. But keep enough control that you’re still building the company you actually want to run, not the one that fits someone else’s portfolio thesis.
There’s a version of ambition that looks like staying profitable and growing steadily rather than chasing valuations and hoping the market cooperates. More founders are choosing it deliberately now, and the results are starting to speak loudly enough that it’s hard to ignore.
The 2021 era convinced a lot of people that fundraising was the goal. It wasn’t. Building something that generates real value is the goal, and it turns out you don’t always need a lead investor and a splashy announcement to do that.
The bootstrapped hybrid model has been here the whole time. It’s just finally getting the audience it deserves. If you’re rethinking your strategy or starting fresh, it might be the most honest framework you’ve come across in a while.
Image by benzoix on Magnific
The post Stop Fundraising Like It’s 2021: The Bootstrapped Hybrid Model Is Quietly Winning appeared first on StartupNation.
2026-04-29 22:45:46
Being a startup founder isn’t all freedom and glory.
Running your own business looks fun from the outside, but startup founders face a lot of hidden costs. These costs sneak in through time, control, health, and identity.
Most advice focuses on success stories. But few talk about what founders really give up to keep the dream alive.
So let’s get real for a minute.
Here are the strategic trade-offs founders need to plan for. 👇
If you’re doing everything yourself (operations, marketing, finances), you end up stuck in the daily grind. You’re working in the business, not on it. This keeps you chasing short-term tasks instead of planning long-term moves, which can slow down your growth potential.
Delegating early isn’t easy. It takes money and trust.
But it frees you to make high-impact decisions. That could mean focusing on revenue and business models, early revenues, or market validation instead of endless administrative work.
The solution: Start delegating early, even small tasks.
Use freelancers or junior hires to handle ops, marketing, or admin work. Schedule “strategy blocks” in your calendar. No emails or meetings allowed during this time. Alongside this, many founders also rely on curated resources like tools for creative strategists to simplify execution without getting pulled back into day-to-day tasks.
function getCountryUnicodeFlag(countryCode) { return countryCode.toUpperCase().replace(/./g, (char) => String.fromCodePoint(char.charCodeAt(0) + 127397)) };
// HTML sanitization function to prevent XSS function sanitizeHtml(str) { if (typeof str !== 'string') return ''; return str .replace(/&/g, '&') .replace(/, '<') .replace(/>/g, '>') .replace(/"/g, '"') .replace(/'/g, ''') .replace(/\//g, '/'); }
// URL sanitization function to prevent javascript: and data: URLs function sanitizeUrl(url) { if (typeof url !== 'string') return ''; const trimmedUrl = url.trim().toLowerCase(); if (trimmedUrl.startsWith('javascript:') || trimmedUrl.startsWith('data:') || trimmedUrl.startsWith('vbscript:')) { return '#'; } return url; }
const getBrowserLanguage = () => { if (!window?.navigator?.language?.split('-')[1]) { return window?.navigator?.language?.toUpperCase(); } return window?.navigator?.language?.split('-')[1]; };
function getDefaultCountryProgram(defaultCountryCode, smsProgramData) { if (!smsProgramData || smsProgramData.length === 0) { return null; }
const browserLanguage = getBrowserLanguage();
if (browserLanguage) { const foundProgram = smsProgramData.find( (program) => program?.countryCode === browserLanguage, ); if (foundProgram) { return foundProgram; } }
if (defaultCountryCode) { const foundProgram = smsProgramData.find( (program) => program?.countryCode === defaultCountryCode, ); if (foundProgram) { return foundProgram; } }
return smsProgramData[0]; }
function updateSmsLegalText(countryCode, fieldName) { if (!countryCode || !fieldName) { return; }
const programs = window?.MC?.smsPhoneData?.programs; if (!programs || !Array.isArray(programs)) { return; }
const program = programs.find(program => program?.countryCode === countryCode); if (!program || !program.requiredTemplate) { return; }
var smsConsentHtmlRenderingFixEnabled = true;
const legalTextElement = document.querySelector('#legal-text-' + fieldName); if (!legalTextElement) { return; }
const divRegex = new RegExp('?[div][^>]*>', 'gi');
const blockWrapperRegex = new RegExp('?(?:div|p)[^>]*>', 'gi');
const fullAnchorRegex = new RegExp('
const template = smsConsentHtmlRenderingFixEnabled ? program.requiredTemplate .replace(/\s*
]*>/gi, ' ') .replace(blockWrapperRegex, '') : program.requiredTemplate.replace(divRegex, '');
legalTextElement.textContent = ''; const parts = template.split(/(.*?)/g); parts.forEach(function(part) { if (!part) { return; } const anchorMatch = part.match(/(.*?)/); if (anchorMatch) { const linkElement = document.createElement('a'); linkElement.href = sanitizeUrl(anchorMatch[1]); linkElement.target = sanitizeHtml(anchorMatch[2]); linkElement.textContent = sanitizeHtml(anchorMatch[3]); legalTextElement.appendChild(linkElement); } else { legalTextElement.appendChild(document.createTextNode(part)); } });
}
function generateDropdownOptions(smsProgramData) { if (!smsProgramData || smsProgramData.length === 0) { return ''; }
var programs = false ? smsProgramData.filter(function(p, i, arr) { return arr.findIndex(function(q) { return q.countryCode === p.countryCode; }) === i; }) : smsProgramData;
return programs.map(program => { const flag = getCountryUnicodeFlag(program.countryCode); const countryName = getCountryName(program.countryCode); const callingCode = program.countryCallingCode || ''; // Sanitize all values to prevent XSS const sanitizedCountryCode = sanitizeHtml(program.countryCode || ''); const sanitizedCountryName = sanitizeHtml(countryName || ''); const sanitizedCallingCode = sanitizeHtml(callingCode || ''); return ''; }).join(''); }
function getCountryName(countryCode) { if (window.MC?.smsPhoneData?.smsProgramDataCountryNames && Array.isArray(window.MC.smsPhoneData.smsProgramDataCountryNames)) { for (let i = 0; i
Wanting to oversee everything feels safe, but it slows your team down.
So does saying yes to every idea. If you approve every feature request, every partnership, every marketing experiment, and every hire suggestion, your team loses focus. Priorities shift constantly. Roadmaps get bloated. And execution gets sloppy. 😖
At some point, business growth demands fewer approvals and clearer ownership.
Founders have to accept less control to let the company scale.
The solution: Define decision rights early.
Being your own boss sounds freeing. In reality, it often means carrying every hard decision alone. Over time, this may lead to loneliness, decision fatigue, and eventually burnout.
Erratic hours and blurred work-life boundaries feel exhausting. But they also affect your judgment, energy, and long-term health. When you’re depleted, your company feels it too.
The solution: Set boundaries early. Define realistic work hours. And protect time that is completely off-limits for work.
This is part of your human capital strategy. You are critical human capital. If you burn out, everything slows down, especially during high-pressure stages like scaling revenue or preparing for Series B. (Leadership skills include emotional regulation and resilience, not just vision and execution.)
Bonus tip: Build a peer circle inside the startup community with founders who understand the pressure. Or work with a mentor who can help you process decisions and manage stress.
Nobody warns you about the paperwork side of being your own boss, and that’s where a lot of founders start drowning. Taxes are way more complicated when you’re responsible for all of it yourself.
It’s not solely income tax either. If your business sells products online, and enough customers in another state start buying from you, you might owe sales tax there even if you’ve never set foot in that state. Rules constantly change, and many small business owners still don’t realize it.
The sales tax considerations include tracking revenue by state, getting permits, figuring out which products are taxable, and remembering different filing deadlines depending on where your customers live. Messing this up can lead to penalties and back taxes.
The solution: Don’t try to wing it. Get help early.
Hiring an accountant or using reliable tax software makes tracking multi-state sales, permits, and filing deadlines way easier. Break it down into steps: Track revenue by state, figure out which products are taxable, and calendar all your deadlines.
Keep records organized and review them monthly so nothing sneaks up on you.
Take free expert-led courses and unlock access to tools, mentorship, networking, and Verizon grant opportunities for small businesses.
A huge hidden cost is tying your self-worth to your startup.
When revenue dips or a pivot fails, it can feel like a personal failure instead of a business adjustment.
When your identity is fused with the startup, decision-making gets distorted. You may avoid necessary pivots because they feel like admitting you were wrong. Or you might overwork to protect your image. This tension eventually shows up in organizational behavior, team relationships, and even how you show up in the startup community.
The solution: Separate who you are from what you’re building.
Make space for interests, relationships, and goals that have nothing to do with your business plan. Talk to mentors or peers who’ve shut down companies, pivoted, or rebuilt after failure.
Journaling with structured reflection can also help you stay grounded. Your goal is building an entrepreneurial mindset that can evolve … without collapsing every time the company changes direction.
One of the most difficult transitions for a startup founder happens when ownership is no longer entirely yours, especially after raising early funding from angel investors or larger institutional investors.
Bringing on venture capital investors, forming a board of directors, issuing stock options, or building an advisory board helps you grow. But they also require you to share control.
On paper, this is progress. In practice, it can feel like a loss.
Equity distribution means that decisions that were once fast and instinctive now require alignment. Your assumptions may get challenged. Your strategy might get questioned. This can surface defensiveness or self-doubt, especially in rooms filled with experienced operators or investors. (Ever seen Shark Tank?)
The solution:
Set transparent expectations around stock options and equity distribution. Define the role of the board of directors versus the leadership team. Use your advisory board for strategic guidance, not operational approval.
Most importantly, separate ownership from identity. Sharing equity doesn’t reduce your importance as a founder. It increases the company’s ability to grow beyond you.
➜ Remember, sustainable scale requires shared leadership.
Being a startup founder comes with perks. But the hidden costs are real. Trading time for strategy, control for scale, and independence for well-being all carry consequences.
Acknowledging them and building support networks, advisory boards, or early hires can help you survive and thrive.
Hitting Series B or growing revenue is great. But keeping yourself and your team intact while doing it is the real win. ❤️
Looking to become a better entrepreneur? Sign up for The Start newsletter. New value drops every Wednesday, directly to your inbox.
Photo by Christina @ wocintechchat.com M on Unsplash
The post The Hidden Cost of Being Your Own Boss Nobody Talks About appeared first on StartupNation.
2026-04-29 05:47:01
Starting a tech company today means working with contradictions. Tools are cheap. Distribution is global. And AI puts serious capabilities in anyone’s hands.
However, the legal landscape shifts faster than most founders expect. And it’s easy to blow past launch milestones without building the foundation that holds up when things get messy.
The legal side works like the backend of your product. Invisible until something breaks, then suddenly everywhere. Read on to learn how to navigate the legal landscape for your tech startup.
Your legal structure defines how you’re taxed and how you raise money. It also determines what happens if things go wrong and how you exit.
Here’s how the common structures compare:
| Business Structure | Definition | Descriptions |
| LLC | Protects personal assets with pass-through taxation |
|
| C-Corp (often Delaware) | A separate, investor-friendly entity taxed on its own |
|
| S-Corp | Pass-through taxation with eligibility limits |
|
| Partnership | Owned by two or more people sharing profits and losses |
|
| Sole proprietorship | A one-person business with no legal separation |
|
To decide, think about:
Legal isn’t just a box to check. It’s part of how you build and scale your startup.
Startup tech trends have taken off since the pandemic. As these trends drive faster innovation and tighter rules, getting the basics right early can save you time. Not to mention money and energy later!
That said, below are legal areas to consider and practical steps to take for your startup.
In tech, intellectual property (IP) can be everything. Think code, models, brand, algorithms, datasets, and designs. However, IP rights protection is one of the common legal issues most small businesses face.
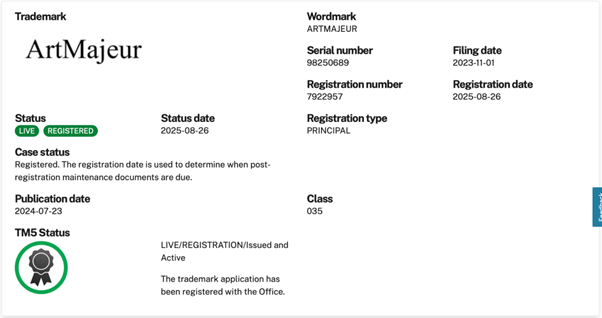
Take it from Samuel Charmetant, founder of ArtMajeur. When launching his art startup, he makes IP rights a top priority to protect pieces of artwork.
“Start documenting innovations from day one and file provisional patents early,” Charmetant suggests. “Too many founders wait, then watch competitors move into their space. A strong IP portfolio protects your position and attracts serious investors.”
The main tools:
Practical protection steps:
Watch out for:
Data flows everywhere now, and regulators noticed. So, there are legal questions to ask when launching your business. Remember, your compliance posture is part of your product.
Compliance isn’t optional anymore. It’s existential. A single GDPR violation can result in fines that sink an early-stage company. Build it into your product development process. Not as an afterthought.
Rules many tech startups face:
Getting practical:
Moving fast doesn’t mean skipping contracts. There are a handful of legal documents you must not ignore.
Eric Yohay, CEO and Founder of Outbound Consulting, sets clear contract agreements for every consulting service rendered. He believes that every little detail should be put into writing.
“Every handshake deal should become a written contract,” Yohay explains. “NDAs protect your ideas during fundraising, service agreements clarify deliverables, partnership contracts prevent future disputes. Invest in proper contracts now to avoid litigation later.”
Must-haves for most tech startups:
Drafting tips:
Mistakes to avoid:
Legal considerations arise when raising capital for your startup. The good news? You’ve got options. Each comes with terms that shape your future more than the headline valuation.
However, understanding term sheets goes beyond valuation. Focus on control provisions and liquidation preferences, and even anti-dilution clauses. These determine who makes decisions and how proceeds get distributed. Smart negotiation today preserves founder control tomorrow.
Common paths:
Legal prep as you raise:
Hiring multiplies legal details fast. Even early on, get the basics right. Legal record-keeping is a must!
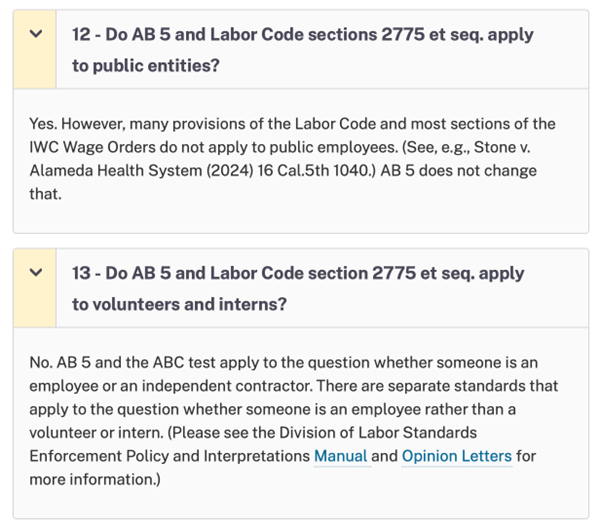
Learn from Andrew Scheidt, General Manager at Central Air Heating, Cooling & Plumbing, who legally complies with employment laws. He has seen the damage employment law violations cause.
“Misclassifying employees as contractors remains one of the biggest legal risks for startups,” Scheidt shares. “The gig economy blurred lines, but the IRS and state agencies enforce strict standards. Proper classification protects both your company and your workers.”
Points to cover:
Your privacy policy is a promise to users and a shield against liability. Clear language about data collection and sharing builds trust while meeting legal requirements. Generic templates won’t protect you, so customize them based on your actual practices.
For instance, TRT online platforms that offer consultations and prescriptions should clearly explain what health data they collect and why they need it. They should also be upfront about sharing data with payment providers and give users a simple way to access or delete their information. Their terms should set clear usage rules, protect their content, and limit liability.
Your privacy policy:
Your terms of service:
A strong legal foundation won’t build your product. It, however, protects the time and money you pour into it. Remember, the goal is spotting risks early and making informed trade-offs. That way, you can stick to your vision while ultimately keeping the company safe enough to grow.
Read this blog to get more insights into starting a tech business. Better yet, sign up for The Start newsletter today!
Image by Drazen Zigic on Magnific
The post Navigating the Legal Landscape: Essential Steps Before Launching Your Tech Startup appeared first on StartupNation.